Your address is like your property address: you must inform men and women what it's to allow them to uncover you. It really is safe To achieve this, since you can still lock your front door with An additional crucial only you Management to ensure that no-a person could possibly get in, even when they know where you reside.
Buyers cannot maintain more than a selected percentage of full supply. Operator can adjust that percentage or disable it. Operator can exclude some accounts with the anti whale mechanism.
By way of seamless token generation, entrepreneurs and enterprises have collectively infused more than $320 million into circulating source globally, fueling expansion and innovation.
Whilst It really is not possible to develop instantly a keys pair with the desired features, the procedure use to generate them can be autonomous enabling a brute-drive approach. Here are the measures I took to generate several vanity addresses.
This venture "profanity2" was forked from the first venture and modified to ensure security by style. This suggests source code of the task never require any audits, but nevertheless assurance Risk-free use.
Hardware Wallets: Components wallets like Ledger and Trezor provide a protected strategy to generate and shop your Ethereum addresses. These Bodily gadgets retain your private keys offline, protecting them from opportunity on the web threats. They provide the next degree of safety in comparison with on the net wallets.
You should utilize exactly the same address on all EVM appropriate blockchains (if you have the kind of wallet that has a Restoration phrase). This list (opens in a fresh tab)
Your address will be the similar in all Ethereum tasks. You don't have to sign-up separately on any undertaking. Once you have a wallet, it is possible to connect to any Ethereum task with none further facts. No emails or almost every other personal information are necessary.
The application will have to generate tokens In line with an ordinary crytptographic algorithm acting to be a proof of the worth nodes are contributing to the applying (Bitcoin utilizes the Evidence of labor Algorithm).
Token supply will probably be 10.000. Your entire token offer might be generated all through deploy and despatched to Token Owner wallet. You can't boost or lessen offer afterwards.
Transaction Execution: Smart contracts are self-executing contracts Together with the conditions from the arrangement specifically written in to the code.
Ensuing private essential needs Check here to be used to be included to seed private critical to accomplish ultimate private important of the specified vanity address (private keys are only 256-bit numbers). Operating "profanity2" may even be outsourced to an individual fully unreliable - it continues to be Secure by design.
Wallet companies don't have custody of your resources. They only supply you a window to find out your assets on Ethereum and applications to simply handle them.
Custom made .i2p area commencing with fabrice. Take note which you can sign up a "regular" area: . The tool is packaged to the AUR but would not compile.
 Angus T. Jones Then & Now!
Angus T. Jones Then & Now! Lark Voorhies Then & Now!
Lark Voorhies Then & Now! Jenna Jameson Then & Now!
Jenna Jameson Then & Now!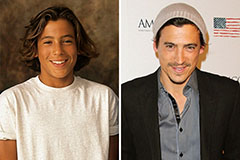 Andrew Keegan Then & Now!
Andrew Keegan Then & Now! Barbara Eden Then & Now!
Barbara Eden Then & Now!